WASHINGTON
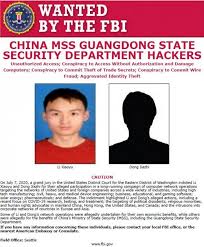
A federal grand jury returned an indictment this month charging two Chinese hackers with hacking into the computer systems of hundreds of victims, according to officials.
 These victims include companies, governments, non-governmental organizations, and individual dissidents, clergy, and democratic and human rights activists in the United States and abroad, including Hong Kong and China.
These victims include companies, governments, non-governmental organizations, and individual dissidents, clergy, and democratic and human rights activists in the United States and abroad, including Hong Kong and China.
The defendants, sometimes, acted for their own personal financial gain, and in others for the benefit of the MSS or other Chinese government agencies.
The hackers stole terabytes of data which comprised a sophisticated and prolific threat to U.S. networks.
The 11-count indictment alleges LI Xiaoyu, 34, and DONG Jiazhi, 33, who were trained in computer application technologies at the same Chinese university, conducted a hacking campaign lasting more than ten years to the present.
They targeted companies in countries with high technology industries, including the United States, Australia, Belgium, Germany, Japan, Lithuania, the Netherlands, Spain, South Korea, Sweden, and the United Kingdom, according to authorities.
Targeted industries included, among others, high tech manufacturing; medical device, civil, and industrial engineering; business, educational, and gaming software; solar energy; pharmaceuticals; defense. In at least one instance, the hackers sought to extort cryptocurrency from a victim entity, by threatening to release the victim’s stolen source code on the Internet.
More recently, the defendants probed for vulnerabilities in computer networks of companies developing COVID-19 vaccines, testing technology, and treatments.
“China has now taken its place, alongside Russia, Iran and North Korea, in that shameful club of nations that provide a safe haven for cyber criminals in exchange for those criminals being ‘on call’ to work for the benefit of the state, here to feed the Chinese Communist party’s insatiable hunger for American and other non-Chinese companies’ hard-earned intellectual property, including COVID-19 research,” said Assistant Attorney General for National Security John C. Demers.

Source: FBI
“Today’s indictment demonstrates the serious consequences the Chinese MSS and its proxies will face if they continue to deploy malicious cyber tactics to either steal what they cannot create or silence what they do not want to hear,” said FBI Deputy Director David Bowdich. “Cybercrimes directed by the Chinese government’s intelligence services not only threaten the United States but also every other country that supports fair play, international norms, and the rule of law, and it also seriously undermines China’s desire to become a respected leader in world affairs. The FBI and our international partners will not stand idly by to this threat, and we are committed to holding the Chinese government accountable.”
According to the indictment, to gain initial access to victim networks, the defendants primarily exploited publicly known software vulnerabilities in popular web server software, web application development suites, and software collaboration programs.
In some cases, those vulnerabilities were newly announced, meaning that many users would not have installed patches to correct the vulnerability.
The defendants also targeted insecure default configurations in common applications.
T he defendants used their initial unauthorized access to place malicious web shell programs (e.g., the “China Chopper” web shell) and credential-stealing software on victim networks, which allowed them to remotely execute commands on victim computers.
he defendants used their initial unauthorized access to place malicious web shell programs (e.g., the “China Chopper” web shell) and credential-stealing software on victim networks, which allowed them to remotely execute commands on victim computers.
To conceal the theft of information from victim networks and otherwise evade detection, the defendants typically packaged victim data in encrypted Roshal Archive Compressed files (RAR files), changed RAR file and victim documents’ names and extensions (e.g., from “.rar” to “.jpg”) and system timestamps, and concealed programs and documents at innocuous-seeming locations on victim networks and in victim networks’ “recycle bins.”
The defendants frequently returned to re-victimize companies, government entities, and organizations from which they had previously stolen data, in some cases years after the initial successful data theft.
In several instances, however, the defendants were unsuccessful in this regard, due to the efforts of the FBI and network defenders.
The indictment charges the defendants with conspiring to steal trade secrets from at least eight known victims, which consisted of technology designs, manufacturing processes, test mechanisms and results, source code, and pharmaceutical chemical structures.
Such information would give competitors a market edge by providing insight into proprietary business plans and savings on research and development costs in creating competing products.